WannaCry Global Infection rate at 11am 16.05.17 AEST
Source: MalwareInt https://intel.malwaretech.com
Supportedge have been monitoring this issue since 12th May 2017.
The good news is none of our clients have reported this infection or system breach to date. The bad news is this is still a big concern.
If we originally setup your network and no changes have been made to the systems we put in place. Supportedge’s security policies have been protecting you from external threats like this.
What is the danger to Supportedge’s clients?
This problem is an issue for Microsoft Windows systems only. The largest risk factor at this stage is an internal infection. If an infected computer is physically connected with a cable or Wi-Fi to your network you must have Microsoft’s security update MS17-010 that was released in March to be protected.
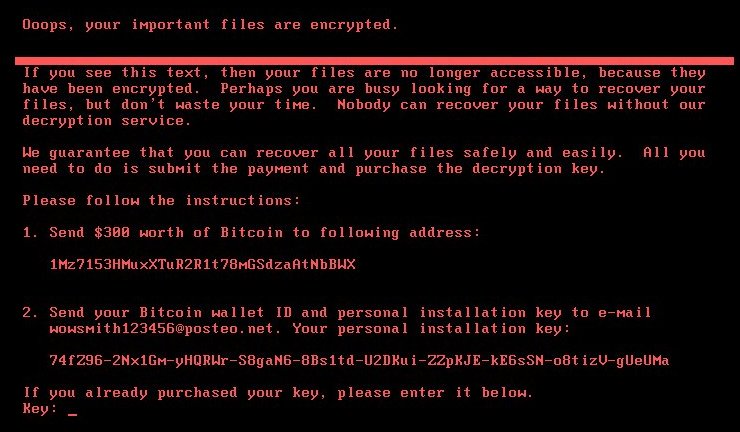
You have seen this cyber security problem in the News. What’s WannaCry (semi-technical)?
WannaCry leverages the ETERNALBLUE exploit. It’s a problem with the way computer systems share files with each other. To prevent penetration, block ports 135, 139 and 445.
What do I do to protect myself?
Call us, we will check your system and report the risk. If you’re a subscription client we have already checked your systems, you don’t need to do anything.
If you’re interested in self-checking your system and you don’t need our help you can find more information and procedures here: https://technet.microsoft.com/en-us/library/security/ms17-010.aspx As a part of your self-checks please also make sure to validate your backups.
I’ve been infected, what now?
First thing is to turn off the infected computer. Most likely the only recovery is your backups. Call us and we will start your system in our security lab so that we can recover your files.
#MalwareTech #Ransomware #CyberSecurity #WannaCry #wannacrypt #supportedge